
Mandated compliance hands criminals your ID. Promised stimulus costs more than it pays. Verified hiring placed enemy operatives. When the system becomes the scam, who do you trust?
GM, Welcome Back to the Dead Drop.
While legislators nationwide celebrate themselves for protecting children online, they've engineered something criminals can only dream of: a legal mandate to collect the most sensitive personal documents in existence.
The Great Government ID Collection Experiment
Twenty-five states have now passed age verification laws requiring Americans to upload government-issued identification to access adult content online. These laws typically mandate verification through digital ID cards, government-issued identification, or commercially reasonable methods based on age and identity verification. Louisiana led this charge in 2022, and the dominoes fell quickly: Texas, Utah, Montana, Virginia, Arkansas, Florida, Kentucky, Alabama, Kansas, Oklahoma, and more joined the parade.
The pitch was simple and emotionally compelling: protect kids from harmful content. The execution? Force platforms to verify every user's age before granting access. Sounds reasonable until you understand what that actually means in operational reality.
These laws mandate age verification through government-issued documents such as driver's licenses, passports, or national ID cards, with failure to verify potentially resulting in millions of dollars in fines. Companies that previously collected minimal user data suddenly face legal requirements to process, store, and protect some of the most sensitive personally identifiable information that exists.
Here's what keeps me up at night: driver's licenses and passports contain everything a professional identity thief needs. Full legal name, date of birth, physical address, government-issued identification number, and in many cases, your photograph. It's a complete identity theft starter kit, now being collected at industrial scale by companies that never wanted this responsibility in the first place.
The Discord Warning Shot
Discord's recent breach exposed government-issued identification documents from users who appealed age-related account suspensions through the platform's verification partner. This wasn't theoretical risk, this was live ammunition proving exactly what security experts warned about.
The breach included typical support ticket data, but one category stood out like a flare in the night: government IDs. Not usernames. Not email addresses. Actual driver's licenses and passports from people who just wanted to prove they were adults.
Organizations now must collect and store volumes of the most sensitive personally identifiable information possible, regardless of whether they have the infrastructure to adequately protect it or even want to collect it. The old cybersecurity principle of minimal data collection becomes legally obsolete when statutes mandate maximum data collection.
AU10TIX: The Breach That Validates Every Warning
AU10TIX, a major identity verification company used by platforms including TikTok, Uber, and X, left login credentials exposed online for more than a year. A researcher gained access to logging platforms containing links to identity documents including names, dates of birth, nationalities, identification numbers, and images of driver's licenses and passports.
Read that timeline again: over a year. This wasn't a sophisticated zero-day exploit requiring nation-state resources. Administrative credentials were stolen by malware in December 2022 and posted to a public Telegram channel in March 2023. For eighteen months, this treasure trove of government identification sat accessible to anyone who knew where to look.
AU10TIX serves some of the world's largest platforms. Millions of identity documents from users who verified themselves on major apps were potentially exposed. This enables phishing, blackmail, identity theft, and complete loss of anonymity and privacy.
The Phishing Gold Mine
Here's where the criminal opportunity gets interesting. Every ID verification mandate creates a legitimate-looking pretext for phishing operations.
Think about the attack vector: you receive an email or text claiming your age verification failed on a platform you actually use. The message looks official because criminals now know which services require verification. The link directs you to a convincing replica site. You upload your driver's license because you've been conditioned that this is now normal, expected, mandatory.
Phishing attacks surged 202% in the second half of 2024, with credential phishing specifically jumping 703%! Users now face an average of one advanced phishing attack per mailbox every week. Every new requirement to upload government IDs trains the public to comply with exactly the type of request criminals exploit.
The AU10TIX breach demonstrates that even when users submit documents to legitimate services, those documents can be compromised. Now imagine how many fake verification services criminals are operating. How many phishing sites perfectly replicate age verification portals. How many databases of government IDs are being assembled by organized criminal networks masquerading as compliance solutions.
The Legislative Blindspot
The widespread hacks and data breaches enabled by age verification laws inevitably will put individuals supplying sensitive personal data at serious risk of identity theft and financial fraud. This isn't speculation from paranoid security researchers. This is documented reality from companies already breached.
Each new database of government IDs becomes a potential breach waiting to happen, and when that breach occurs, damage extends beyond immediate victims to include regulatory penalties, litigation, reputation damage, and loss of customer trust.
Legislators designed these laws with good intentions, but they failed to account for operational reality in threat environments. They mandated data collection without mandating corresponding security infrastructure. They created legal liability for non-compliance while simultaneously creating massive attack surfaces that guarantee future breaches.
The Fraudfather Bottom Line
Age verification laws have transformed the internet into a massive government ID collection operation with inadequate security controls. Every verification requirement creates new phishing opportunities. Every centralized database becomes a target. Every breach exposes complete identity theft packages.
You cannot legislate away the fundamental security principle that sensitive data attracts sophisticated attackers. You cannot mandate perfect protection for imperfect systems. And you cannot train an entire population to routinely upload their government identification without also training them to fall for phishing attacks that exploit that exact behavior.
The criminals are watching these laws pass, and they're preparing infrastructure to exploit them at scale. They understand something legislators apparently don't: when you force millions of people to upload their most sensitive documents to verify their age, you create the world's largest, most valuable, legally mandated honeypot.
Stay sharp. Trust slowly. Verify everything, especially requests for your government ID.
Got a Second? The Dead Drop reaches 5,250+ readers every week including security professionals, executives, and anyone serious about understanding systemic wealth transfers. Know someone who needs this intelligence? Forward this newsletter.

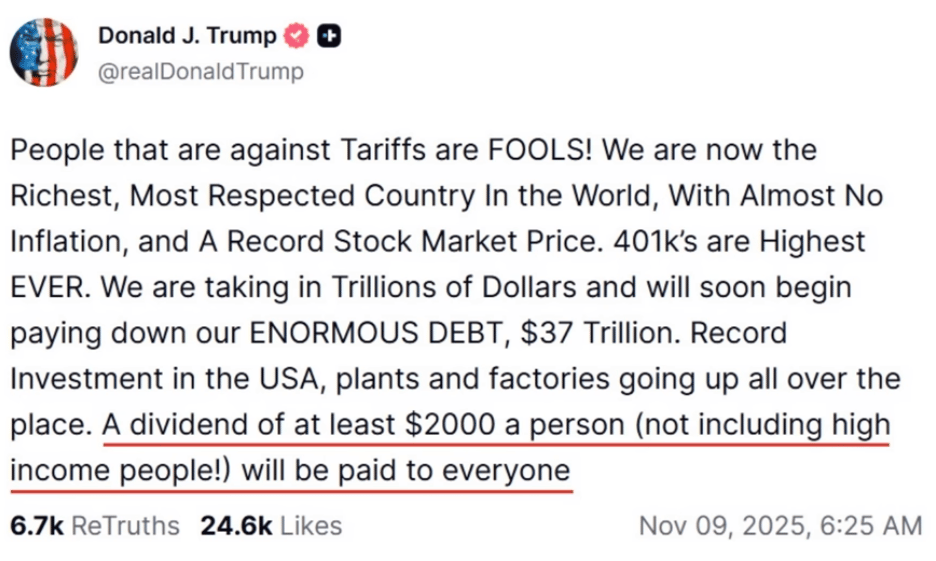
The $2,000 Check Illusion: How You're Funding Your Own Stimulus
President Trump just promised Americans a $2,000 "tariff dividend," claiming massive income is pouring in from foreign countries to fund it. Here's what two decades investigating financial fraud taught me: when someone promises you free money while misdirecting where it's actually coming from, you're the mark in a con.
Let me show you the sleight of hand.
The Fundamental Lie
Trump's pitch sounds compelling: foreign countries pay tariffs, we collect massive revenue, and Americans get $2,000 checks from this windfall. It's clean. It's patriotic. It's completely backwards.

Here's what the law actually says, straight from Title 19 of the U.S. Code governing Customs Duties: "The fee charged shall be paid by the importer of record of the merchandise." Not the exporter. Not foreign governments. Not Chinese or Mexican companies. The American importer pays the tariff.
When Walmart imports goods from China, Walmart pays the tariff. When Target brings in products from Vietnam, Target pays the tariff. When your local retailer stocks shelves with imported inventory, that retailer pays the tariff. Every single time, it's an American company writing the check to the U.S. Treasury.
This isn't opinion. This isn't political spin. This is federal statute.
The Pass-Through You're Already Paying
Now here's where the fraud accelerates. Do you believe for one second that Walmart, Target, Amazon, or any other importer is absorbing these costs out of the goodness of their corporate hearts? They have shareholders demanding profits and balance sheets requiring protection.
The tariff becomes a tax on American consumers, passed through retail pricing with mathematical certainty. Walmart raised prices. Target raised prices. Amazon raised prices. Nike, Adidas, Home Depot, Macy's, AutoZone, and Best Buy all raised prices on tariff-affected products. This already happened. You're already paying higher costs.
Look at the evidence in your grocery cart. The government claims inflation is running at 3%. Meanwhile, banana prices are up 8.6% year over year. Coffee prices surged 40%. Why? Because these products are heavily imported, and importers passed tariff costs directly to consumers.
You cannot economically grow bananas in Chicago. You cannot harvest coffee beans in Nebraska. These necessities require imports, which means they require tariffs, which means Americans pay elevated prices for basic goods while being told foreign countries are funding the bill.
The Math That Doesn't Math
Let's examine the financial mechanics of this promised dividend. Tariffs are projected to collect just under $300 billion for the entire 2025 calendar year. That's the total revenue coming in from these import taxes that you're paying through higher retail prices.

A $2,000 stimulus payment to every eligible American costs approximately $600 billion. The Congressional Budget Office calculated that the $1,400 stimulus check issued in 2021 cost $411 billion. Simple multiplication tells you that a $2,000 payment requires substantially more.
So we have $300 billion in tariff revenue and a $600 billion stimulus cost. Even if you were terrible at mathematics, you can see this equation doesn't work. And remember, Trump also promised to use "leftover" tariff money to "substantially pay down national debt."
There is no leftover. There's a $300 billion shortfall before you even consider debt reduction.
The Supreme Court Wild Card
Here's the variable that could collapse the entire scheme: Trump implemented these tariffs without Congressional approval, which normally would be required. The Supreme Court is currently reviewing whether these tariffs are legal.
If the Court rules that tariffs require Congressional votes, most of Trump's tariff regime gets struck down immediately. That $300 billion revenue projection drops below $100 billion. Your promised $2,000 check vanishes, but you'll keep paying the elevated prices that companies already implemented.
You get the inflation without the compensation.
The Classic Misdirection
This is textbook fraud psychology. Promise people money. Tell them someone else is paying for it. Make them feel like they're getting something for nothing. Meanwhile, they're funding their own supposed windfall through higher costs on everything they buy.
The scheme works because of psychological distance. When you pay $6 for bananas instead of $5.50, you don't immediately connect that to tariff policy. When your coffee costs 40% more, you blame the coffee company, not import taxes. When Target raises prices across departments, you shop somewhere else, but everywhere else raised prices too.
The financial damage gets distributed across thousands of small transactions, making it invisible while remaining absolutely real.
The Fraudfather Bottom Line
Foreign countries don't pay American tariffs any more than American companies pay foreign taxes. Importers pay tariffs, then pass costs to consumers with markup. You're funding the
se tariffs through elevated prices on everything from food to clothing to electronics to household goods.
If you receive a $2,000 stimulus check, understand this: you already paid for it multiple times over through the inflation tax that tariffs created. The government isn't giving you free money from foreign countries. They're returning a fraction of what they extracted from your wallet, then telling you to be grateful for the rebate.
This isn't wealth redistribution from foreign nations to American citizens. It's wealth extraction from American consumers, laundered through import taxes, with a promised rebate that mathematics says can't possibly materialize as advertised.
You're not getting paid a dividend. You're getting back crumbs from money that was yours to begin with, after it took a round trip through elevated retail prices
The best marketing ideas come from marketers who live it.
That’s what this newsletter delivers.
The Marketing Millennials is a look inside what’s working right now for other marketers. No theory. No fluff. Just real insights and ideas you can actually use—from marketers who’ve been there, done that, and are sharing the playbook.
Every newsletter is written by Daniel Murray, a marketer obsessed with what goes into great marketing. Expect fresh takes, hot topics, and the kind of stuff you’ll want to steal for your next campaign.
Because marketing shouldn’t feel like guesswork. And you shouldn’t have to dig for the good stuff.
The Fraudfather's take on the week's biggest scams, schemes, and financial felonies, with the insider perspective that cuts through the noise.
When Your IT Recruiter Is Actually a North Korean Intelligence Asset
Five people just pleaded guilty to something that should terrify every hiring manager, HR professional, and business owner in America: helping North Korean operatives infiltrate 136 U.S. companies and funnel $2.2 million directly to Kim Jong Un's weapons program. Four Americans and one Ukrainian didn't hack systems or steal data in the traditional sense. They did something far more insidious: they opened the front door and invited the threat inside.
Here's what keeps me awake: one of these facilitators was an active-duty U.S. Army servicemember at the time. Alexander Paul Travis earned over $51,000 helping North Korean IT workers steal American identities, pass employment background checks, and even take drug tests on their behalf. Let that sink in: a member of our military, trusted with national security, was literally appearing for urinalysis screenings so North Korean intelligence operatives could get remote jobs at U.S. firms.
The Recruitment Pipeline You Never Saw Coming
The traditional narrative focuses on North Korean hackers breaking into systems. This isn't that. This is exponentially more dangerous because it exploits the weakest link in every organization's security: the hiring process.
The operation works with surgical precision. North Korean operatives based in China and Russia create sophisticated fake profiles using stolen American identities. Ukrainian national Oleksandr Didenko specialized in exactly this: stealing U.S. citizens' identities and selling them to North Korean IT workers. He helped infiltrate 40 U.S. companies and agreed to forfeit $1.4 million as part of his guilty plea. Eighteen Americans had their identities stolen and weaponized in these schemes.
But identity theft is just phase one. The real genius is what happens next: laptop farms. Companies ship brand-new laptops to what they believe are domestic addresses. Americans like Erick Ntekereze Prince hosted these machines at residences across Florida, installing remote desktop software so North Korean operatives could access corporate networks while appearing to work locally. Prince ran his operation through a company called Taggcar Inc., positioning himself as a legitimate IT staffing firm. He earned $89,000 while helping North Korean workers generate over $943,000 in salary payments.
Your Recruiter Might Be Working for Pyongyang
Here's the angle that should make every professional recruiter's blood run cold: North Korean operatives aren't just applying for jobs anymore. They're now posing as recruiters themselves, creating fake recruiting firms and job placement agencies that Fortune 500 companies hire without realizing they're contracting with North Korean front operations.
Security researchers have documented North Korean actors creating listings for positions like "Virtual Assistant" and "Customer Support" on platforms like Virtualstaff.ph and Onlinejobs.ph. These aren't job postings; they're recruitment channels to find Americans willing to become facilitators. The conversations follow predictable patterns: financial struggles, promises of easy money for minimal work, and step-by-step instructions on how to help overseas workers appear domestic.
The scheme scaled because of human nature. These facilitators weren't sophisticated criminals; they were ordinary Americans facing financial pressure. One case involved an Arizona woman who posted on TikTok about her struggles, lost her job, burned through savings, and eventually lost her house while working as a laptop farm operator. The North Koreans specifically target people in vulnerable financial positions because desperation makes compliance easier.
The Ransomware Evolution Nobody Anticipated
The financial threat just scratched the surface. Security researchers now confirm that North Korean IT workers, once embedded in companies, are escalating to data theft and ransomware. They request elevated network privileges, exfiltrate proprietary information, and demand payment to prevent leaking stolen data to competitors or selling it on dark web markets. One contractor stole company information almost immediately after being hired.
This isn't hypothetical. CrowdStrike tracked 304 incidents involving North Korean IT workers in 2024 alone, with activity accelerating in the second half of the year. Microsoft discovered that between 2020 and 2022, over 300 U.S. companies, including multiple Fortune 500 firms, unknowingly employed these operatives. SentinelOne tracked roughly 360 fake personas submitting over 1,000 job applications to their company alone.
The threat evolved beyond detection. These operatives use AI to enhance stolen identity photos, voice-changing software during interviews, and real-time AI assistance to answer technical questions. They work in teams, coaching each other through video interviews when candidates can't avoid turning on cameras. They've created complete operational playbooks on identity theft, creating freelancer profiles, and bidding on projects.
The Professional Risk You Can't Outsource
Every IT staffing firm, recruiting agency, and HR department now faces an impossible calculation: the people applying for your jobs might be generating revenue for a hostile nuclear power. The person you're interviewing might have an entire team in Pyongyang feeding them answers. The resume you're reviewing might be completely fabricated using stolen credentials. The recruiter offering you "certified" IT workers might be running a North Korean front operation.
This isn't a cybersecurity problem; it's a human intelligence operation executed at scale against American business infrastructure. The facilitators who pleaded guilty proved something crucial: North Korea doesn't need to hack your systems when they can convince Americans to hand over access voluntarily.
The Justice Department seized $15 million in cryptocurrency alongside these guilty pleas, but that barely touches the estimated hundreds of millions North Korean IT workers generate annually. Every dollar funds weapons programs. Every data theft advances military capabilities. Every infiltration creates intelligence collection opportunities against U.S. companies and technologies.
Your next IT hire could be funding nuclear weapons development. Your recruiting partner could be a North Korean intelligence front. And somewhere in America right now, there's a laptop farm hosting dozens of corporate machines, all connected to operatives working from China, Russia, or North Korea itself.
The facilitators are being prosecuted. The question is: how many more haven't been caught yet?
The Fraudfather combines a unique blend of experiences as a former Senior Special Agent, Supervisory Intelligence Operations Officer, and now a recovering Digital Identity & Cybersecurity Executive, He has dedicated his professional career to understanding and countering financial and digital threats.
This newsletter is for informational purposes only and promotes ethical and legal practices.





