🚨 You Are the Product: Google, Fingerprinting, and the New Age of Digital Surveillance 🚨
If you feel like privacy is dying, that’s because it is—and the ones who promised to protect and preserve it are the ones driving the knife in.
Google just greenlit device fingerprinting, a tracking method so precise it makes cookies look like medieval tech. VPNs? Useless. Incognito mode? A joke. Even if you change networks, clear your data, and swear off the internet, Google can still recognize you.
And they’re not alone. Apple fingerprints your spending habits through Apple Pay. Social media tracks you whether you’re logged in or not. Your "private" transactions are quietly tying your real-world identity to your online behavior.
This week, we break down how they’ve rewritten the rules—and how you can stop being an easy mark.
In this week's issue:
🔹 Google’s Fingerprinting Power Grab – They once called it a violation of user privacy. Now, they’re all in. Surprise, surprise.
🔹 The VPN Delusion – Still using a VPN and thinking you're anonymous? You're not. Here's why.
🔹 Apple’s Privacy Lie – How Apple fingerprints your spending, location, and habits while pretending to protect you.
🔹 Le Roux: The Criminal Genius Who Might Be Bitcoin’s Creator – A coder-turned-warlord who ran his empire like a Fortune 500 CEO—except his board meetings ended with bodies.
🔹 Machiavelli’s Playbook for Power – How to stop being a pawn and start playing the game.
The Fraudfather’s Note:
The problem isn’t that you’re being tracked. The problem is that you’re being conditioned to accept it.
They give you privacy settings—but never a real option to opt out. They let you disable tracking—but keep logging you anyway. They tell you it’s for security—but it’s really about control.
The digital panopticon isn’t coming. It’s here.
But here’s the good news: systems have loopholes. Surveillance has blind spots. And power always has a weakness.
The question isn’t if you’re being watched.
The question is: How do you make sure they don’t like what they see?
Let’s get to work.
📞 Need a privacy overhaul? Book a Call with the Fraudfather! to fortify your defenses today!
"From working around a few U.S. Presidents, I learned this: The greatest con isn’t theft—it’s conviction. They don’t just take your money; they rearrange your reality until you applaud them for the privilege of being robbed."
Fraud’s Hall of Infamy: The Week’s Top Villain
Google’s New Privacy Villain Arc: Tracking You, Whether You Like It or Not
In a plot twist worthy of a cyberpunk dystopia, Google has finally dropped the pretense of caring about your privacy. Starting February 16, the tech giant will allow advertisers to track you via device fingerprinting, a method they themselves once condemned as a "subversion of user choice." But hey, that was 2019 Google—this is 2024 Google, and now they’ve decided you don’t get a say.
The excuse? Smart TVs, gaming consoles, and streaming services are too lucrative to ignore, so Google is greenlighting cross-platform surveillance under the guise of "improving ad effectiveness." Translation: They’re ensuring that whether you're watching Netflix on your TV, browsing Amazon on your phone, or doom-scrolling in incognito mode, advertisers can still piece together who you are, what you want, and exactly how much you’re willing to pay for it.
And here’s the kicker: Unlike cookies (which you can at least delete), fingerprinting can’t be turned off. Your device’s unique hardware and software quirks—screen resolution, installed fonts, even the way your processor handles JavaScript—become an inescapable tracking beacon. Google will now happily pass this data to advertisers, data brokers, and who knows who else.
Remember when Google was a search engine? Yeah, neither do they. Welcome to the future, where you are the product, and opting out isn’t an option.
📞 Book a Call with the Fraudfather! to fortify your defenses today!
Futureproofing Fraud Defenses
The VPN Delusion: Why Your Privacy Play is Already Compromised
They sell you the dream of invisibility—anonymity wrapped in encryption, a tunnel through which your digital self supposedly vanishes. “Buy this VPN,” they whisper, “and reclaim your privacy.” But here’s the problem: the game changed while they were still selling you 2010’s security playbook.
Your IP address is only one piece of the puzzle, and a VPN alone is like hiding your house key under the doormat—it gives you the illusion of safety while the real threats are already inside.
Enter device fingerprinting, the silent killer of online anonymity when used incorrectly.
Modern tracking technologies have rendered VPNs little more than digital costumes—sufficient to fool amateurs, but utterly useless against adversaries who actually understand how to identify, track, and monetize your data. If you think you’re covering your trail with a VPN, you’re not anonymous—you’re just an easier mark for those who actually know what they’re doing.
Let’s dismantle the fraud of VPN-based security and expose why the real war for privacy has moved far beyond just changing your IP.
1. The Great IP Diversion—How VPNs Trick You Into Feeling Safe
VPNs operate under one seductive promise: if they can’t see your IP, they can’t track you. This is the kind of half-truth that makes a great marketing slogan but a terrible security strategy.
🔹 Here’s the problem: Your IP address is just one piece of data in a much larger tracking system. Fingerprinting tools don’t need your IP when they have your device’s unique configurations, browser quirks, and hardware signatures to follow you like a bloodhound.
Modern tracking systems can recognize you even if you switch VPNs every five minutes, because your machine itself is the giveaway—the fonts you have installed, the way your GPU renders a webpage, the size of your screen, the browser extensions you use. It’s all logged, categorized, and indexed.
🚨 Your Hack: If you want actual anonymity, start thinking beyond your IP. Use tools like Brave browser’s fingerprint randomization, Firefox’s hardened privacy settings, or specialized browsers like Mullvad to rotate fingerprints and break tracking chains.
2. Device Fingerprinting: The Ultimate Online Surveillance Weapon
If VPNs are the security equivalent of a Halloween mask, fingerprinting is facial recognition on steroids. It’s a set of advanced tracking techniques designed to make you identifiable even if you rotate IPs, use incognito mode, and wipe your cookies after every session.
Advanced fingerprinting methods analyze:
Your browser’s canvas rendering signature (a unique digital “smudge” created by your GPU)
Your installed fonts, language settings, and operating system
Your audio processing quirks (yes, even your computer’s sound system leaks unique data)
Your WebGL and graphics card identifiers
By collecting dozens of these data points, fingerprinting systems assign you a persistent digital identity—one that follows you across devices, VPNs, and network changes.
🚨 Your Hack: The best defense isn’t just avoiding fingerprinting—it’s poisoning the data. Tools like Brave’s anti-fingerprinting mode, the CanvasBlocker extension for Firefox, and browser virtualization through Whonix create inconsistent, unpredictable fingerprints, making tracking you an absolute nightmare.
3. Apple: The Privacy Hypocrite
Apple tells you they care about your privacy. They tell you they don’t track you. But what they do tells a different story.
🔹 Here’s how they actually fingerprint you:
Apple Wallet & Device Association: Every time you use Apple Pay, your device ID and payment details are linked. This isn’t just for security—it’s a persistent tracking method that ties your purchases to your specific device, allowing Apple to build an intimate profile of your spending habits.
Bluetooth & Location Beacons: Your iPhone constantly pings nearby Bluetooth and WiFi signals, even when you think you’ve disabled location tracking. Apple cross-references these signals with time-stamped transactions to map out your pattern of life—where you go, when you go there, and what you’re likely to spend.
Private Relay Is a Controlled VPN: Apple’s "Private Relay" sounds like a privacy feature, but in reality, it’s just a VPN with an Apple chokehold. They still see the metadata, control the relays, and maintain the ability to flag and track "suspicious" activity. You aren’t disappearing—you’re just trusting Apple instead of your ISP.
🚨 Your Hack: If you use Apple devices, assume everything is being logged. Disable Apple Pay unless necessary, turn off Bluetooth scanning in privacy settings, and use a dedicated, non-Apple payment method for sensitive purchases.
4. The Lie of "Security Through Obscurity"
Most people operate under the naive belief that being one of billions of internet users makes them unimportant. This is the ostrich approach to privacy: bury your head in the sand and hope no one notices.
🔹 Reality check: Modern data collection isn’t about following one person. It’s about pattern recognition, clustering, and predictive analytics. If you think your digital footprint is insignificant, congratulations—you’re exactly the kind of passive target that AI-driven tracking systems love.
🚨 Your Hack: Take control of your operational security (OpSec). Never log into personal accounts while using privacy tools. Never reuse device setups across different activities. Use multiple browsers, multiple devices, and dedicated virtual machines for sensitive actions.
5. Real-World Exploits: How Fingerprinting Makes Fraud & Hacking Easier
Most VPN marketing campaigns focus on evading governments and ISPs, but they rarely talk about how VPNs fail completely against actual threats—hackers, scammers, and digital predators.
🔹 Example #1: Fraud Detection Systems
Banks and financial institutions use fingerprinting to catch fraudsters by recognizing devices across multiple accounts. If you’re running fraud ops? Forget VPNs—your machine fingerprint alone can link accounts, flag transactions, and lock you out permanently.
🔹 Example #2: AI-Powered Tracking
Fingerprinting isn’t static—it’s evolving. Machine learning models actively correlate mouse movement behavior, typing cadence, and website navigation patterns to build user profiles in real-time. You might think you’re anonymous, but your own habits betray you.
🔹 Example #3: Malware and Account Takeovers
Let’s say a hacker compromises your email but doesn’t log in right away. Instead, they analyze your device fingerprint—then spoof it before accessing the account. Your bank or service provider, instead of flagging the login, thinks you just logged in.
🚨 Your Hack: Always assume that anonymity is an arms race. Mask your fingerprint, randomize your behavior, and avoid using any one device for too long in the same pattern.
6. Business Owners, Marketers, and CISOs—Here’s What You Should Do
Fingerprinting isn’t just a tool of surveillance—it’s also a powerful weapon for fraud prevention, security, and marketing optimization. If you run a business, whether in e-commerce, finance, or cybersecurity, you should be using fingerprinting to protect your company.
🔹 Business Applications:
✅ Fraud Prevention: Block multi-account fraud, bot activity, and suspicious login attempts before they escalate.
✅ Enhanced Security: Identify high-risk logins even if credentials are correct by recognizing unauthorized devices.
✅ Optimized Marketing: Track real users across sessions without cookies, gaining deeper insights into customer behavior.
🚨 Need help integrating fingerprinting into your stack? I can teach you how to deploy high-level device fingerprinting strategies to boost security, stop fraud, and optimize conversions.
Historical Insight
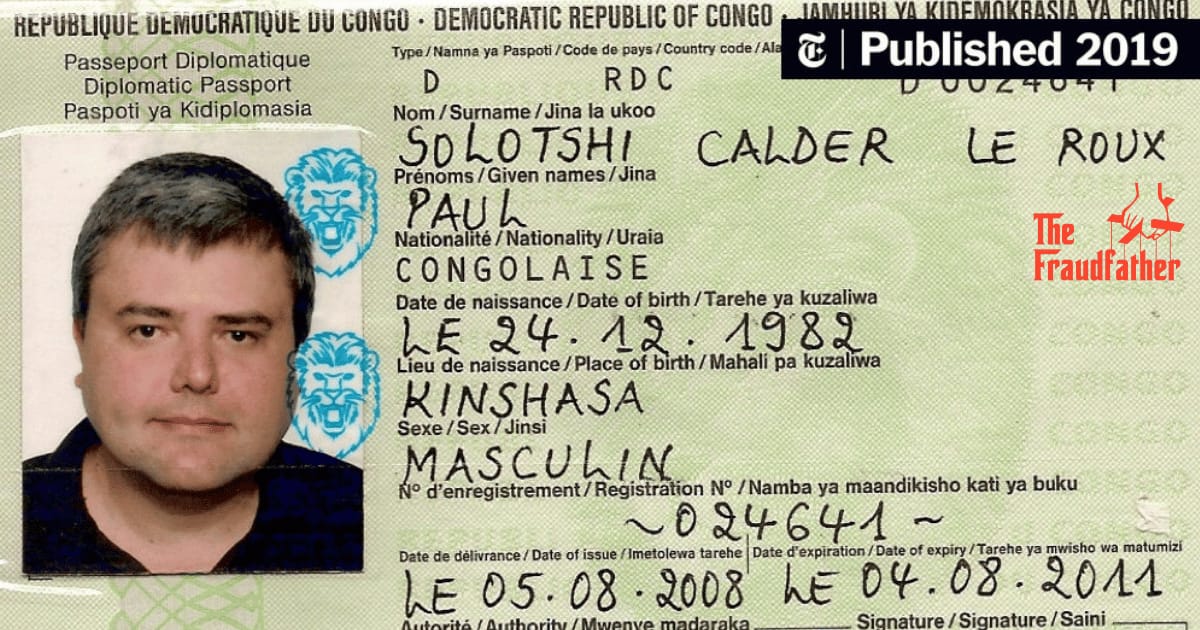
The Ghost in the Machine: Paul Le Roux and the Blueprint for Power, Fraud, and the Future of Crime
Some men break the law. Some men rewrite it. Paul Le Roux didn’t just game the system—he was the system. A former coder who built encryption software, he flipped the script, turning his genius toward smuggling, arms trafficking, money laundering, and cold-blooded murder.
From shipping meth out of North Korea to orchestrating assassinations like a warlord with an IT department, Le Roux ran his empire like a Silicon Valley CEO—except his board meetings ended with bodies, not stock options. He wasn’t just ruthless. He was efficient.
And if that wasn’t enough, some believe he’s Satoshi Nakamoto, the architect of Bitcoin. Whether true or not, the fact that it's even plausible tells you everything you need to know about the way he operated.
But forget about the myth for a second. Let’s talk about the method.
Le Roux’s tactics weren’t just for crime. They were strategies—ones that governments, businesses, and power players use every day. The difference between a cartel and a corporation? A few legal loopholes and some well-placed PR.
This week, we’re tearing apart Le Roux’s blueprint—not to run a criminal empire, but to run circles around anyone who doesn’t understand the real rules of power.
1. Be Everywhere and Nowhere – The Power of Invisible Influence
Le Roux never had a physical headquarters, no empire to raid, no office doors to kick down. His businesses spanned continents, his employees often had no idea who they were working for, and his actual name rarely appeared on anything.
🔹 Your Hack: Control from the shadows. Whether in business or influence, the smartest operators don’t advertise their position—they let others take the spotlight while they pull the strings. If you’re the face of an operation, you’re also the first target when things go south. Influence is strongest when it’s invisible.
The Ghost in the Code: Paul Le Roux and the Art of Playing the System
Some men break the law. Some men rewrite it. Paul Le Roux didn’t just game the system—he was the system. A former coder who built encryption software, he flipped the script, turning his genius toward smuggling, arms trafficking, money laundering, and cold-blooded murder.
From shipping meth out of North Korea to orchestrating assassinations like a warlord with an IT department, Le Roux ran his empire like a Silicon Valley CEO—except his board meetings ended with bodies, not stock options. He wasn’t just ruthless. He was efficient.
And if that wasn’t enough, some believe he’s Satoshi Nakamoto, the architect of Bitcoin. Whether true or not, the fact that it's even plausible tells you everything you need to know about the way he operated.
But forget about the myth for a second. Let’s talk about the method.
Le Roux’s tactics weren’t just for crime. They were strategies—ones that governments, businesses, and power players use every day. The difference between a cartel and a corporation? A few legal loopholes and some well-placed PR.
This week, we’re tearing apart Le Roux’s blueprint—not to run a criminal empire, but to run circles around anyone who doesn’t understand the real rules of power.
1. Be Everywhere and Nowhere – The Power of Invisible Influence
Le Roux never had a physical headquarters, no empire to raid, no office doors to kick down. His businesses spanned continents, his employees often had no idea who they were working for, and his actual name rarely appeared on anything.
🔹 Your Hack: Control from the shadows. Whether in business or influence, the smartest operators don’t advertise their position—they let others take the spotlight while they pull the strings. If you’re the face of an operation, you’re also the first target when things go south. Influence is strongest when it’s invisible.
2. Legitimacy is Just a Smokescreen – The Art of the Gray Area
Le Roux didn’t start out with a gun to his head—he started with an online pharmacy that operated in a legal gray zone. By the time he was moving cocaine and weapons, he still maintained the illusion of a legitimate businessman. Most of his early wealth came from selling prescription drugs legally—until the definition of legality changed.
🔹 Your Hack: Find the cracks in the system. Whether it’s regulation, finance, or technology, the people who win are the ones who find legal gray areas before anyone else. If a market is under-regulated, there’s an opportunity. If a system is outdated, there’s leverage. And by the time the world catches up? You’ve already made your move.
3. Fear and Greed: The Twin Levers of Control
Le Roux kept his mercenaries in check with absolute fear. But he kept his bankers, arms dealers, and suppliers in line with unlimited greed. People either feared what would happen if they crossed him, or they were too busy counting their cut to care.
🔹 Your Hack: Control behavior by understanding motivation. Everyone moves because of one of two things: the promise of reward or the fear of loss. Scarcity, exclusivity, and FOMO drive action as much as threats do. Know which button to press, and you’ll never need brute force.
4. The First Rule of Power: Own the Infrastructure
People who play small think about the product. The real players think about the system. Le Roux wasn’t just selling drugs—he built an entire logistics empire that moved cash, arms, and information across borders like FedEx for criminals.
And if the Bitcoin rumors are true? That would mean he built a global financial weapon long before anyone knew what it was.
🔹 Your Hack: Don’t just play the game—own the board. In business, if you control the supply chain, the data, or the platform itself, you’re untouchable. The biggest companies don’t just sell—they create dependence. If your customers, clients, or competitors need you to function, you don’t compete. You dictate.
5. The Narrative is the Reality
Even after his arrest, Le Roux kept control of the story. For years, his own employees thought he was still in charge. He let rumors spread. He created doubt. And in a world where perception is reality, that was all he needed.
🔹 Your Hack: Frame the conversation before someone else does. If you control how people think about a situation, the facts don’t even matter. In negotiations, deals, or influence, set the mental frame before the other side even knows they’re playing.
6. The Perfect Exit – Always Have an Escape Plan
Le Roux’s real genius wasn’t in what he built—it was how he burned it down when it suited him. When the walls closed in, he flipped the script, snitched on his own people, and walked away with 25 years instead of life. Some of his lieutenants got longer sentences than he did.
🔹 Your Hack: Never play a game you can’t exit on your own terms. The real winners aren’t the ones who fight to the last breath. They’re the ones who have the option to walk away untouched. Always build your position with an exit in mind. If you can’t control when or how you leave, you’re not really in charge.
The Fraudfather’s Take: Play Smarter, or Get Played
Paul Le Roux wasn’t just a criminal—he was a systems thinker who understood leverage better than most Fortune 500 CEOs. The difference? He applied his strategies to the underworld instead of Wall Street.
But the tactics? They’re the same ones used in business, politics, and power struggles every single day.
✅ Invisible control is the best control. The most powerful people are the ones you don’t even realize are pulling the strings.
✅ Own the system, not just the product. When people rely on you, you don’t need to compete—you dictate the rules.
✅ Fear and greed run the world. Understand what drives people, and you’ll never need brute force.
✅ Control the narrative, control reality. If you set the frame, the facts don’t matter.
✅ Always have an escape plan. The strongest position is the one where you can leave anytime, on your terms.
Le Roux played the game at a level most people will never understand. His only mistake? He played on the wrong side of the law.
Because the real players?
They’re not in prison. They’re running hedge funds, global corporations, and political campaigns.
Cognitive Insights

"Power isn’t taken—it’s orchestrated. Machiavelli plays the long game, where kings and pawns alike dance to the will of the true master.”
Cognitive Insights: Machiavellian Hacks for a Rigged System
Power doesn’t belong to the righteous—it belongs to the strategic. Fraudsters, politicians, and market manipulators know this, and they play the game accordingly. The weak? They moralize. The powerful? They adapt.
Machiavelli understood that influence is war, deception is a tool, and truth is optional. The real fraudsters aren’t the ones running small-time scams—they’re the ones rewriting the rules of reality while the rest of the world clings to outdated notions of fairness.
Here’s how you don’t get played.
1. The Illusion of Virtue: Perception is Reality
📖 “A prince must appear to be virtuous, but he must be willing to act against virtue when necessary.”
Fraudsters don’t succeed because they’re smart; they succeed because they look the part. The most dangerous players—be they scammers or CEOs—aren’t obvious villains; they’re the ones who borrow prestige, curate credibility, and make you want to believe in them.
🔹 Your Hack: Master the art of borrowed prestige. Align yourself with powerful institutions, respected individuals, or high-status brands. If people trust the source, they’ll trust you. Build an aura of credibility so strong that no one even thinks to question you.
2. The Power of Fear: Control Through Uncertainty
📖 “It is better to be feared than loved, if you cannot be both.”
Fraudsters use charm first. If that fails? Fear. The same logic applies to influence. Markets don’t move on logic—they move on fear of missing out, fear of risk, and fear of failure. The biggest businesses don’t sell products; they sell security against an imagined loss.
🔹 Your Hack: Leverage controlled urgency. Deadlines, exclusivity, and scarcity force action. Whether it’s a high-stakes deal, a negotiation, or a sales pitch, make your audience feel the cost of inaction more than the promise of reward.
3. Win Before the Battle: Pre-Suasion & Narrative Control
📖 “Never attempt to win by force what can be won by deception.”
Fraudsters don’t sell outright lies—they prime their targets. By the time the pitch comes, the victim has already convinced themselves. The best manipulators in history—from financial scammers to Silicon Valley visionaries—didn’t push their message. They framed reality itself so that their version was the only one that made sense.
🔹 Your Hack: Set the mental frame before presenting your ask. The greatest negotiators, salespeople, and power players don’t argue; they lead people to a conclusion that feels like their own idea. Manipulators use this to deceive. You’ll use it to dominate.
4. Exploiting Human Weakness: The Bandwagon Effect
📖 “The great majority of mankind are satisfied with appearances, as though they were realities.”
Cassie Chadwick didn’t convince a few banks—she convinced one. Then, the rest followed. People don’t fact-check; they assume that if everyone else believes something, it must be true. This is why frauds like Theranos lasted as long as they did—because perception creates reality.
🔹 Your Hack: Create momentum. Stack social proof. Get a few high-status endorsements, let others spread the hype, and watch people rush to join the crowd. Make belief contagious.
5. The Art of Ethical Ruthlessness
📖 “A prince must not mind incurring the reproach of cruelty when it is necessary to keep his subjects united and faithful.”
Fraudsters justify their actions because it gets them what they want. You don’t need deception, but you do need strategic detachment. In a world where power is a zero-sum game, hesitation is defeat.
🔹 Your Hack: Master ethical ruthlessness. Know when to cut losses, eliminate liabilities, and take actions others won’t. Fraudsters manipulate without remorse. You? You’ll make the hard choices because you understand the game.
6. Always Own the Infrastructure
📖 “Whoever is responsible for another’s power ruins himself.”
Real power isn’t in building something great—it’s in controlling what others rely on. Amazon doesn’t own e-commerce; it owns the infrastructure that makes it possible. Google doesn’t just provide search results; it dictates what is search.
🔹 Your Hack: Don’t just play in a system—own the leverage points. In business, this means controlling distribution channels, data, or resources others depend on. In influence, this means shaping the conversations people think they’re choosing.
The Fraudfather’s Take: Power Belongs to Those Who Take It
Machiavelli wasn’t writing a manifesto for fraud—he was writing a survival guide for anyone who refuses to be a pawn.
The modern world is run by people who understand these rules. Politicians, executives, and influencers don’t win because they’re the best; they win because they create the conditions for victory before the game even starts.
This isn’t about deception—it’s about mastery.
A con artist weaponizes these principles for personal gain.
A strategist?
They weaponize them to reshape the world.
Which one are you?
📞 Book a Call with the Fraudfather! to fortify your defenses today!
About The Fraudfather
The Fraudfather combines a unique blend of experiences as a former Senior Special Agent, Supervisory Intelligence Operations Officer, and now a recovering Digital Identity & Cybersecurity Executive, He has dedicated his professional career to understanding and countering financial and digital threats.
Fast Facts Regarding the Fraudfather:
Global Adventures: He’s been kidnapped in two different countries—but not kept for more than a day.
Uncommon Encounter: Former President Bill Clinton made him a protein shake.
Unusual Transactions: He inadvertently bought and sold a surface-to-air missile system.
Perpetual Patience: He spent 12 hours in an elevator.
Unique Conversations: He spoke one-on-one with Pope Francis for five minutes using reasonable Spanish.
Uncommon Hobbies: He discussed beekeeping with James Hetfield from Metallica.
Passion for Teaching: He taught teenagers archery in the town center of Kyiv, Ukraine.
Unlikely Math: Until the age of 26, he had taken off in a plane more times than he had landed.
📞 Book a Call with the Fraudfather! to fortify your defenses today!
This newsletter is for informational purposes only and promotes ethical and legal practices.



